Authenticate 2023: Day 2 Recap

By: FIDO Staff
Day 2 of Authenticate 2023 was another day packed full of sessions, with a strong emphasis on how organizations across different industries have been able to implement and benefit from strong authentication and passkeys.
The opening keynotes for the day focused on what is needed for widespread deployment of passwordless authentication standards including FIDO and passkeys.
Anna Pobletts, Head of Passwordless at 1Password, used her time on the keynote stage to highlight the important role that credential managers can play in improving user experience and accessibility. Pobletts noted that credential managers provide a familiar experience for passkey authentication in browsers. She said that since introducing passkey support last month, 1Password has seen over 150,000 users create over 300,000 passkeys.

“We’re all working together to make this passwordless future real, companies like Google, Apple, Microsoft, the major platforms have this enormous reach, they can reach billions of people,” Pobletts said. “They have this ability to educate the masses in a way that, quite frankly, credential managers never will, but on the other hand, we can really help with adoption among our customer bases by meeting them where they’re at.”
Dealing with the challenges of scale and usability
Rolling out strong authentication and passkeys at massive scale is a topic that experts from Amazon and Google also detailed during the morning keynotes.

Mike Slaugh, principal industry specialist at Amazon, discussed the challenges of scaling authentication systems to support billions of global users. He said that when talking about scaling, there is an increase in users, complexity within the environment, and more ways of authenticating with more authentication methods. He also joked that edge cases like authenticating “hermits who live in caves” become real use cases at global scale. To address complexity, Slaugh recommended simplifying systems.
“Complexity is the enemy of scale,” he said. “The more complex you get, the more of a house of cards you’re building.”
He proposed viewing authentication as a lifecycle from identity verification to enrollment to authentication to recovery. Giving users choice in authentication methods can also improve throughput.
Mitch Galavan and Court Morgan from Google detailed a different challenge, that of optimizing usability at scale. The two Googlers shared insights into designing passkey authentication for users to help improve usability.

Galavan explained that at Google, convenience is key for users. So at every part of the passkey experience, the mission is to build it with a core of simplicity. Getting it simple though has been an iterative process where Google has worked to make it as easy as possible for users to understand and use. It’s an effort that has paid off.
Test results showed users found passkeys easier to use than their previous sign in method and that they “feel more secure with passkeys.” Morgan noted that once users try passkeys, 76% are likely to use them again.
User stories at Authenticate 2023 take flight
Air New Zealand, FOX, Shopify and Pinterest were among the large organizations that spoke in sessions on Day 2 of Authenticate 2023, providing insights into the strong authentication landscape.

Anthony Kemp, product platform owner for IAM at Air New Zealand, detailed how the airline has been able to use FIDO strong authentication and passkeys to improve user experience and even save money. Key benefits included a dramatic reduction in account recovery requests.
The ease of use also ended up helping to drive sales, because there wasn’t as much user drop-off during the authentication phase and users were more eager and able to buy travel.
“That was great because I’m in cyber, and cyber never makes money and never saves money,” he said.
Media conglomerate FOX Corporation has also benefited from FIDO. Dean Perrine, the company’s deputy CISO, was very enthusiastic about the benefits of FIDO authentication as a way to help reduce authentication risk. Perrine said that FOX has over 12,000 users that needed to be protected and buying YubiKeys for all of them and getting it deployed is a process that takes time but there was user demand for the approach.

Integrating some applications to work with FIDO wasn’t hard, as FOX was able to use standards based approaches with existing identity providers. Integrating non-standard applications that didn’t work with an existing identity system was a challenge and one that FOX solved by working with solution provider Cerby. Fox now has over 7,100 users connected to FIDO2 based factors across non-standard applications.
The ins and outs of social authentication at Pinterest
Euccas Chen, senior software engineer at Pinterest, explained in a session how the social media sharing site has been improving its authentication efforts in recent years.
“Every day millions of people across the globe log into Pinterest and they might have different types of devices and they might experience various types of network conditions,” Chen said. “That translates to millions of authentication events. You can imagine how imperative it is for us to keep the user authentication both smooth and secure.”
One increasingly popular option used at Pinterest is to support sign up using other social accounts, including Facebook, Google and Apple. She used most of her time on stage to detail the rigorous steps taken to secure the social login, including taking steps to secure application level credentials and also protect third party API calls.
Shopify details the pitfalls of SMS based authentication
A common approach used for multi-factor authentication is the use of one time tokens sent via SMS. It’s an approach that Avhinav Lele, staff security engineer at Shopify, isn’t all that enthusiastic about.
Lele noted that SMS is easy as a second factor because everyone has a phone, which is why it has been a popular option. That said, he detailed numerous risks including SIM wapping, social engineering, SMS toll fraud and other attacks.
During the session he also detailed the high costs associated with SMS based on authentication as telecom providers need to get paid for sending messages as well as registering numbers and short codes.
The view from the U.S. Government
Authentication is a big topic within the U.S government and a panel of officials took the stage at Authenticate 2023 to provide insights.
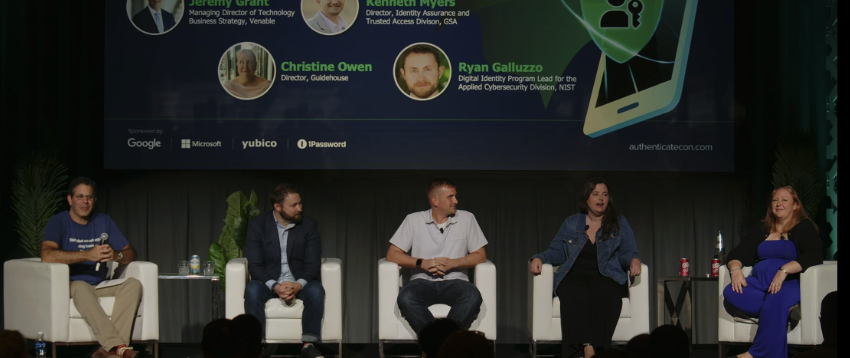
NIST is actively working on multiple publications for guidance that helps government as well as private sector organizations to implement strong authentication. Ryan Galluzzo, Digital Identity Program Lead, Applied Cybersecurity Division at NIST, noted that there is some coming guidance about synced passkeys.
Kenneth Myers, director at U.S. General Services Administration (GSA) talked a bit about how his agency has been able to push FIDO adoption with an effort referred to as, committees of action. The groups are made of six to eight U.S agencies that are actively running FIDO pilots. He noted that approximately 17 agencies have gone through the process so far including the US Department of Agriculture (USDA) which is pushing out FIDO as an authenticator to its 110,000 person workforce.
Authentication in the Payments Industry
The last session of the day was a panel of payment industry experts gathered to discuss the evolution of authentication and its impact on fraud mitigation.
While there has been progress, there is also frustration that fraud persists at all levels of the payment ecosystem, including even basic check fraud.
“We keep acting like it’s so sophisticated and we keep making it even faster and faster and more remote, but we can’t even get the basics fixed, so that’s my view of payments,” Kim Sutherland, VP of Fraud and Identity Strategy at LexisNexis Risk Solutions said.
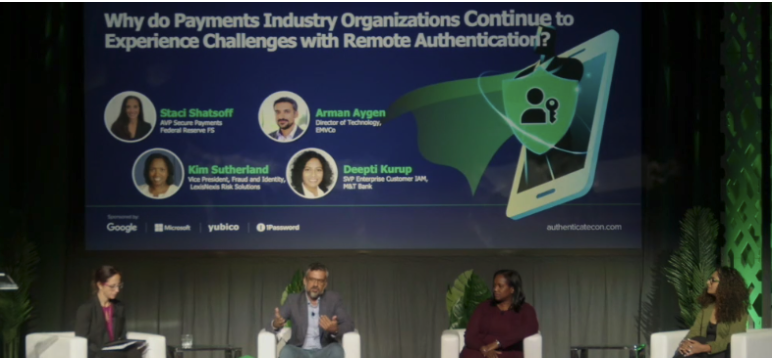
Introducing friction into the payments process isn’t necessarily a bad thing, according to Deepti Kurup, SVP Enterprise Customer IAM at M&T Bank. She noted that in her view, now is the right time to focus on consumer education and helping them to understand that friction is not always a bad situation. She added that helping consumers to understand that when things are happening without friction, that there are really strong authentication methods that are happening passively as well, and they just might not understand.
There are many different components that can work together to help reduce payment fraud and strong authentication from FIDO is part of the mix. Arman Aygen, Director of Technology at EMVCo, explained that his organization collaborates with the FIDO Alliance and the W3C in a web payment security interest group.
“We’ve been focusing on how the different technologies can work together,” he said.Day 3 of Authenticate 2023 is underway on October 18, and if you missed Day 1 be sure to check out the recap here. To register to join the conference in Carlsbad or attend remotely, visit authenticatecon.com.