FIDO Alliance Announces Agenda for Authenticate APAC 2026
Global innovators from Adidas, Apple, Grab, OpenAI, Samsung Electronics and more to share expertise at Singapore authentication & identity event
Singapore, April 30, 2026 – The FIDO Alliance today announced the agenda for Authenticate APAC 2026, a conference bringing together global leaders to advance secure, simple and trusted technologies for authentication and identity. This inaugural APAC event marks the first time Authenticate will be held in the region, building on seven years of successful Authenticate events in the United States and two years of regional FIDO APAC summits.
Authenticate APAC 2026 will take place June 2–3, 2026 at the Grand Hyatt Singapore and is supported by Signature Sponsors Google, Visa and Yubico.
Designed for business leaders, security professionals, and product innovators, the program combines technical depth with real-world deployment insights and forward-looking perspectives on the evolution of digital identity and trusted interactions.
Authenticate APAC 2026 offers a unique opportunity to hear directly from organizations deploying modern authentication and identity technologies at scale, gain practical insights on implementing passkeys, and explore the current state of digital credentials, AI and agent-driven capabilities – and what’s needed to advance adoption. It also provides a clear view into how evolving standards, regulations and new use cases are shaping the future of trusted identity-related interactions across APAC and beyond.
Agenda highlights include:
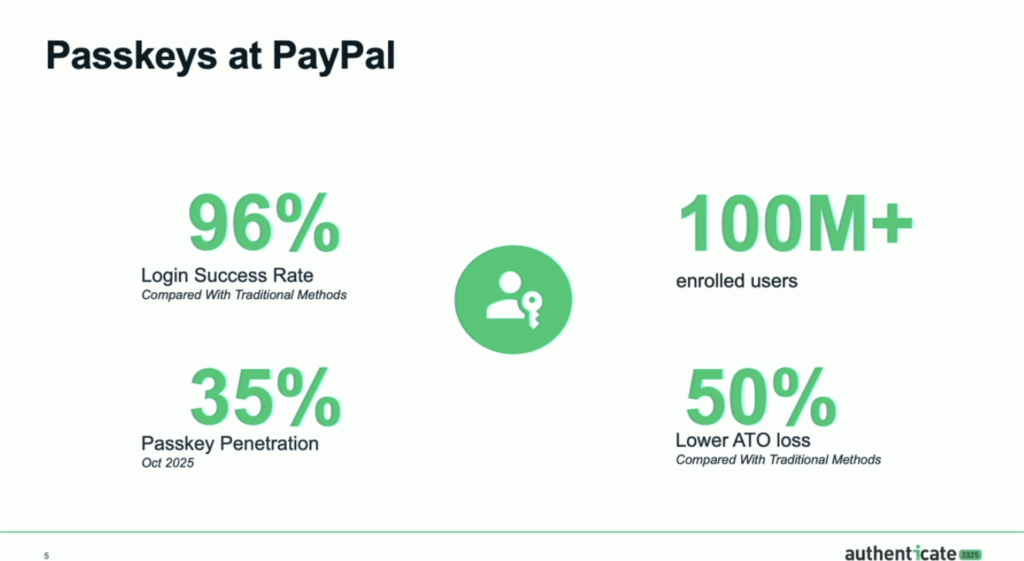
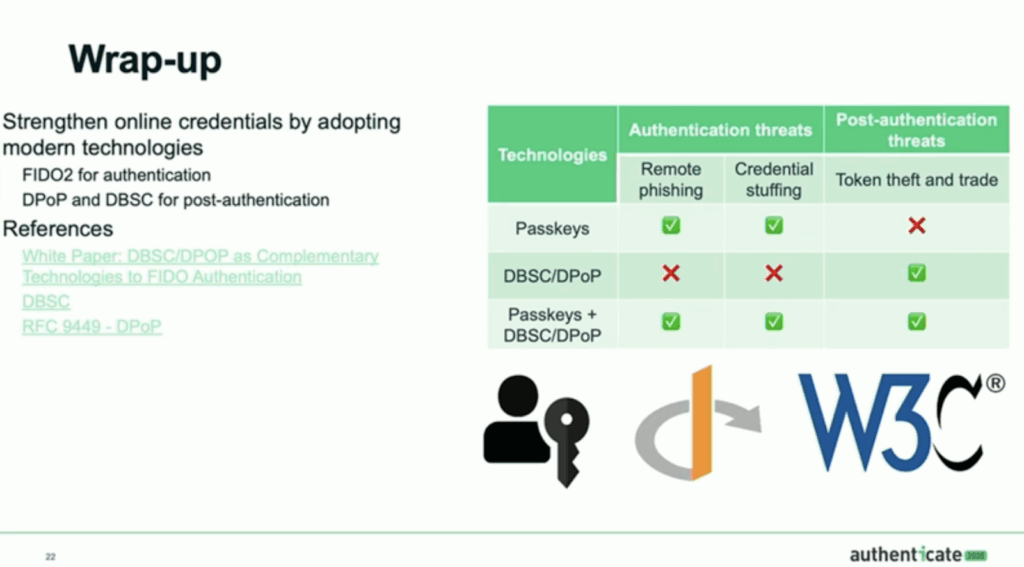
- Authentication standards and best practices, including the latest on passkeys
- The intersection of authentication and AI
- Agentic authentication and agentic commerce
- Digital credentials, wallets and payments
- Enterprise passkey deployments at scale
- Regional regulatory developments and considerations
- Emerging use cases and the future of authentication
In addition to keynote presentations and breakout sessions, attendees will have opportunities to connect with peers and industry experts through dedicated networking events and an active expo hall.
Visit https://authenticatecon.com/event/authenticate-apac-2026/ to view the full agenda and to register.
Sponsorship Opportunities Available
Authenticate offers unique sponsorship opportunities for companies to showcase solutions to an engaged, decision-making audience. Prospective sponsors can learn more and apply at https://authenticatecon.com/sponsors/ or contact [email protected].
About Authenticate APAC 2026
Authenticate is the premier conference dedicated to advancing digital identity and authentication, with an emphasis on phishing-resistant sign-ins using passkeys. Hosted by the FIDO Alliance, this inaugural Asia-Pacific event marks the first time Authenticate will be held in the region. The event brings together CISOs, security strategists, product managers and identity architects to explore best practices, technical insights and real-world case studies in modern authentication. The Authenticate APAC 2026 conference will take place from June 2-3, 2026 at the Grand Hyatt Singapore, followed by the FIDO Alliance member-only plenary on June 4-5.
Signature sponsors for Authenticate APAC 2026 are Google, Visa and Yubico.
Authenticate Contact
[email protected]
PR Contact
[email protected]