Authenticate 2021: Day Two Recap

The second day of Authenticate 2021 was a full day of keynotes, sessions and panels about the continuing progress and opportunities for FIDO authentication, digital identity and a passwordless future.
The day started with a rousing keynote from Microsoft outlining how the tech giant is looking to end passwords.
“About a month ago, we actually announced in our consumer practice that you can now delete passwords all together from your account, and only use strong authentication,” Pamela Dingle, Director of Identity Standards at Microsoft said. “In doing that you’re deleting the risks and frustrations that come with passwords.”
The risks that come from passwords is a topic that Microsoft has researched at great length in its latest Microsoft Digital Defense Report. Dana Huang, Director of Engineering for Enterprise and Security at Microsoft Azure, noted that according to the report, phishing attacks are responsible for 70% of the breaches that Microsoft is seeing. On the more positive front, Microsoft has also observed a huge increase in adoption of strong authentication over the past year of 220%.
While some organizations and users might think they aren’t at risk from a phishing password related attack, Dingle emphasized that every account matters.
“Now you may have to take a triage type of approach to strong authentication, you may have to start with your administrators,” Dingle said. “But the truth is that any account that can be compromised can become a wedge by which an attacker can move laterally across your enterprise.”
Visa’s Passwordless Strategy
Moving to a world without passwords is also a key strategy for David Henstock, Head of Product, Identity and Authentication at Visa.

“When it comes to authentication, what we want to do is pretty simple, we want you to forget about passwords,” Henstock said. “We want to get passwords out of our ecosystem.”
Henstock added that countless studies have proven that knowledge based authentications don’t work and it’s nearly impossible for the consumers to juggle password managers.
“We just need a better way, and FIDO, we believe is that way,” Henstock stated emphatically.
Hacking MFA
Not all Multi-factor authentication (MFA) technologies are the same and in fact most non-FIDO methods are potentially hackable, according to Roger Grimes, defense evangelist at KnowBe4.
Grimes noted that attackers are not necessarily directly attacking MFA solutions, but rather are often phishing the human that is using MFA, in an attempt to bypass the normal execution of MFA.
“With an MFA attack the really common approach is to convince the victim to visit a fake website through an email or social media,” Grimes said. “So the victim thinks that they’re going to a site that they intend to go to that they’re going to log on to using multi factor authentication, and what the attacker does is trick them into going to some man in the middle proxy website.”
Somewhat ironically, Grimes emphasized that the whole reason many organizations are going to MFA is to try and limit the risk of social engineering phishing attacks. In his view it is incumbent on organizations to choose the right strong authentication approach to limit phishing risk.
Certification is a Hot Topic at Authenticate 2021
Certification was the topic of a number of sessions on day two of Authenticate 2021. Dr. Rae Rivera, Certification Director for the FIDO Alliance, outlined the value of certification in an afternoon session.

Rivera also discussed a number of new certification efforts including the FIDO Certified Professional and the Document Authenticity Certification. She explained that the FIDO Certified Professional is about helping organizations that want to deploy FIDO so they can hire professionals that are knowledgeable.
The Document Authenticity Certification is a bit of a different type of effort for FIDO, which is generally more concerned about authentication, though in recent years identity and authentication have become increasingly intertwined. What has also become apparent is the need for standards based certification efforts for documents that are used to help authenticate and verify user identity.
During a panel session about the document authentication certification effort, Stephanie Schuckers, Professor at Clarkson University, explained the constituent components of the initiative. There’s the document authentication component and then there’s the face verification piece .
“Essentially what the goal is is when you take a photograph of a document, you’re trying to determine, is this a legitimate document and you’re trying to gather information from the document,” Schuckers explained.
With the face verification piece, which can involve a selfie image, the document authentication certification effort will attempt to verify how well the selfie image matches the face, gathered from the document. Additionally, she noted the certification will require a liveness piece to make sure the selfie image is of a real live person, and not just a reproduction or fake.
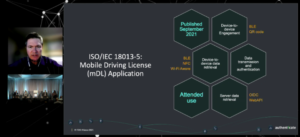
The topic of having a digitally verified form of identity was also part of a panel discussion on mobile driver’s licenses (mDLs). David Kelts, Director of Product Development for Mobile ID at GET Group, commented that today there are already tens of thousands of mDL holders in pilot or pre-production and hundreds of thousands in pilots expected in 2022.
While mDLs are for motor vehicle operation, Kristina Yasuda, Standards Architect at Microsoft, observed that just like the physical form of driver’s licenses, they will also be useful for other types of identity use-cases, including age verification.
User Experience is Key to FIDO Success
No matter how good FIDO based technology is, it’s no good if users don’t adopt it. That’s an area that goes beyond just technology, to understanding and optimizing the user experience, which was the topic of several sessions.

Kevin Goldman, Chief Experience Officer at Trusona, observed during a session that for designers and application teams, it’s often viewed as being easier to just have a username and a password, as that’s what they have always done and the tooling and workflows are long established.
“So, there’s friction, not only in the end user experience that we need to solve for, there’s also friction in the experience of the makers,” Goldman said.
The FIDO Alliance recognized that user experience (UX) matters and established a task force in 2020 to create guidance on how it can be optimized to be easier for both end users and the makers. The guidance is now publicly available at: fidoalliance.org/ux-guidelines
“As an anecdote of all the work I’ve done at FIDO this project was probably the coolest thing,” Andrew Shikiar, Executive Director and CMO of FIDO said. “We have a lot of security and authentication identity experts but actually working with capital D designers and UX people is really important.”
Bringing FDO to the Internet of Things
FIDO Authentication helps to enable users to authenticate services and a new effort is now going to help enable authentication for onboarding of Internet of Things devices and sensors.
David Turner, Director of Standards Development at the FIDO Alliance, explained that the FIDO Alliance launched the IoT Technical Working Group (IoT) TWG in June 2019 to help solve the challenge of device onboarding. Intel contributed their Secure Device Onboard specification which served as a starting point for what is now known as the FIDO Device Onboard Specification (FDO) specification.
“We’re basically looking at drop shipping a product, having someone receive it and physically put it wherever it’s going to go, turn it on and have it connect automatically with no other human interaction required,” Turner said.
User Stories: Target and Wayfair
Among the users that spoke on day two were Target and Wayfair.

Tom Sheffield, Senior Director of Cybersecurity at Target, explained that his company has been on a FIDO adoption journey for several years as the retailer looks to enhance security.
“We recognize the inherent weaknesses in passwords, the need for strong authentication capabilities and we want to improve user experience,” Sheffield said. “We want to increase productivity, while also enabling our team members to do their job securely, and in a compliant way as secure by default is our design pattern.”
One of the areas where Target is deploying FIDO is for its own operations. With a deployment of biometric, fingerprint authentication devices, Target has been enabling FIDO based strong authentication across its internal applications. Sheffield said that over 99% of his users have been able to register for, and leverage fingerprint ID, without needing to engage any help desk support.
A key thing for Target’s deployment was making it understandable and attractive to users. To that end, Sheffield emphasized that words matter.
“We didn’t say password less, because we’re not getting rid of passwords, at least yet,” Sheffield said. “Nor did we say Fido, because it is a dog’s name, and it’s an unknown term outside of the identity community.”
For Mike Virginio, Senior Manager, Corporate Security Engineering at Wayfair, words also matter. Like Target, Wayfair is using FIDO to help secure its operations, including corporate headquarters, call centers as well as warehouses. Wayfair stated on its FIDO journey in 2019, not to be passwordless, but rather to just use less passwords in its operations, to help reduce the risk and operational hassles.

One thing that Virginio experienced that he wasn’t quite expecting was that there were people within Wayfair that actually liked using passwords.
“It was shocking because my whole life I’ve heard that passwords stink, and they’re hard to use and remember and so on,” Virginio said. “But it is something that’s very familiar, people understand how it works and there are recognized support mechanisms for them that have been used for a long time.”
To help get past that resistance he suggested that implementers be transparent about the technology that is being rolled out and create articles, user guides and diagrams that explain what FIDO strong authentication is all about.
“Coming to the table prepared and having those diagrams and so on, ahead of time is really helpful,” Virginio said.
Day Three is Loaded with Content
Day Three of Authenticate 2021 gets underway on Oct. 20 with sessions from Google and Amazon Web Services kicking off the day. User stories are also plentiful with sessions from the Cambridge Housing Authority and the New York Air National Guard among others.
There is also a not to be missed panel on the intersection of Zero Trust and authentication. And of course there’s the party!