Authenticate 2022: Day 2 Recap

By: FIDO Staff
The second day of the Authenticate 2022 conference had a mix of topics and speakers that spanned multiple facets of the authentication world including payment security, biometrics, national identity and design systems.
The day got started with a keynote from Doug Fisher, senior director at Visa, who discussed the current state of the global payments system and the challenges it faces. Fisher noted that while ecommerce fraud remains a pervasive risk, strong online authentication is helpful to help reduce that fraud.
A challenge for stronger forms of authentication for ecommerce is often that it introduces more friction into the consumer buying process, which can lead to shopping cart abandonment. To help solve that issue, Fisher explained that the FIDO Alliance, EMVCo and the W3C have been working together to help improve interoperability in a bid to reduce payment authentication friction. The joint effort had led to the Secure Payment Confirmation (SPC) standard that is currently in development
“SPC is a web standard currently in development that is built on WebAuthn to support streamlined authentication during a payment transaction,” Fisher said. “SPC and FIDO go together like peanut butter and jelly.”
The perils of MFA
Not all multi-factor authentication (MFA) technologies are equal was the primary message in a session led by Roger Grimes, data-driven defense evangelist at KnowBe4.
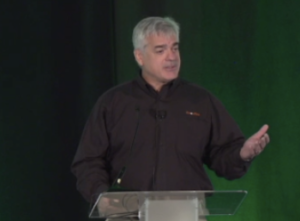
Grimes outlined a litany of MFA bypass techniques that could potentially enable attackers to exploit vulnerable users. He emphasized however that FIDO based strong authentication is unlike MFA in that it can help to eliminate many of the man-in-the-middle attacks that enable bypassing techniques.
“MFA attacks have been around for decades but it certainly is going mainstream this year,” Grimes said.
The risks of non-FIDO MFA is top of mind for Heikki Palm Henriksen, CTO of BankID.

Henriksen’s organization provides a digital identification that is widely used in Norway. BankID started to look at FIDO in 2020 and discovered the insightful white papers produced by the alliance which helped Henriksen and his team to choose FIDO and begin implementation.
“We realized that FIDO2 was the best solution to modernize BankID to reach our goals,” Henriksen said.
Biometric considerations for FIDO
Strong authentication can make use of biometrics such as a fingerprint reader or facial recognition system, as an authenticator.
Biometric systems however are not universally without fault or bias, which is an issue that was discussed by Stephanie Schuckers, director, Center for Identification Technology Research (CITeR) at Clarkson University.
“When we talk about bias related to biometrics, what we’re really talking about is variability in performance due to demographics or demographic differentials,” she said.
Shuckers emphasized that bias relates to the specific technology implementation being used, not the whole field of biometric recognition. Through testing and certification, it is possible to better understand and reduce the risk of potential bias.
Greg Cannon, principal AI/ML standards at Amazon joined Schuckers for a panel session, emphasizing that the goal is to help eliminate passwords and biometrics is a great technology for doing that.
To help illustrate the point that biometrics spoofing is a concern that testing can help to solve, Shuckers brought some props on stage, including a mask of her own face, which apparently did not fool the facial detection system on her phone.
Consumer authentication habits
Understanding how users view authentication is an important aspect of understanding what needs to be done to help improve adoption.

The FIDO Alliance conducts an annual survey that looks at consumer habits for trends and adoption of authentication technologies. Megan Shamas, senior director of marketing at FIDO Alliance, said that the 2022 survey shows users are in some respects entering their passwords less than prior years, though the data is far from being definitive.
Perception of biometrics is also re-assuring as a potential way to help eliminate the use of passwords.
“We have actually been very pleased with consumer sentiment towards biometrics,” Shamas said. “In fact, a lot of consumers that we surveyed find it to be the most secure way to log in.”
Helping to reduce remote authentication fraud
Marianne Crowe, vice president, secure payments innovation and research at Federal Reserve Bank of Boston, used her time on stage to ask for more cooperation across the authentication ecosystem to help secure against fraud.
Crowe noted that there is consumer fatigue with passwords and many users will just reuse the same passwords on multiple sites which is an unsafe practice. MFA is helpful, but she noted that it is often inconsistent today in how it is presented to consumers.
“We’ve got to try to increase implementation and adoption of MFA even in industries and businesses that aren’t required to do it,” Crowe said.
Design system comes to FIDO
One of the ways consistency can come to authentication and specifically to FIDO based strong authentication is with the use of a design system.
Organizations can now benefit from the FIDO design system at fidoalliance.org/design-system that provides principles, patterns and reusable components.
“Our intention for putting all this together is to make FIDO deployments simpler and faster for product designers, for project managers, product managers and engineers,” Kevin Goldman, chief experience officer at Trusona, said. “Our intention is to fill the gaps that they might have around authentication in their own design systems.”
The final day of Authenticate 2022 is looking to be another day loaded with useful content, thoughtful discussion, more user stories and best practices to help organizations move to the passwordless future.Want to attend the final day of Authenticate 2022? Registration for virtual attendance is still available, and all registrants have access to past sessions on demand. To register, visit www.authenticatecon.com.